Encrypted Document & Passwords – Severing the Head From the Body
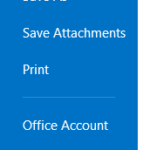
For users of any current versions of Acrobat (Pro, Cloud, or similar versions), securing a PDF attachment with a password is relatively simple. You open the File menu, select properties, navigate to the “securities” tab, and change the document security settings by clicking add “password security”. From here, you can add a password to open the document, print the document, do assembly functions, or restrict editing. You can choose whichever options you want (just keep in mind that you want your user to be able to do what they need to do also).